A new build has been released to Fast Ring Insiders for Windows 10. This time, it’s build 18945. If you got the accidentally released build 18947 build earlier this week, it’s best to rollback to the previous build and then install this one. What’s new in this build? A new Cortana experience, Windows Subsystem for Linux improvements, updated file explorer search, and more.
Be sure to check out the known issues in case there is a show stopper for you.
Known Issues
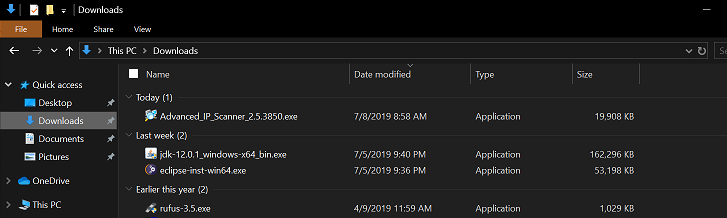
- There has been an issue with older versions of anti-cheat software used with games where after updating to the latest 19H1 Insider Preview builds may cause PCs to experience crashes. We are working with partners on getting their software updated with a fix, and most games have released patches to prevent PCs from experiencing this issue. To minimize the chance of running into this issue, please make sure you are running the latest version of your games before attempting to update the operating system. We are also working with anti-cheat and game developers to resolve similar issues that may arise with the 20H1 Insider Preview builds and will work to minimize the likelihood of these issues in the future.
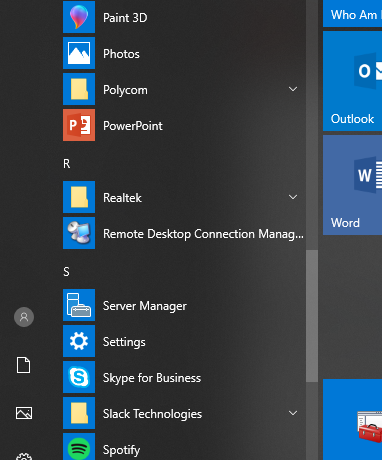
- Some Realtek SD card readers are not functioning properly. We are investigating the issue.
- Tamper Protection may be turned off in Windows Security after updating to this build. You can turn it back on. In August, Tamper Protection will return to being on by default for all Insiders.
- Occasionally, the candidate selection in prediction candidate window for the Japanese IME doesn’t match with the composition string. We are investigating the issue.
- Insiders may notice some changes in Magnifier with today’s build. These aren’t quite ready yet for you to try, but we’ll let you know once they are in an upcoming flight.